The sextortion spam that is prominent today has existed for many months now, if not longer. We’ve written about it ourselves in our April post (https://spamauditor.org/2018/04/no-they-didnt-catch-you-masturbating/). However, we understand most people are not up to date with Information Security news, so this article will provide a summary on sextortion spam and the different iterations that we have encountered so far during our spam auditing.
The Meaning of ‘Sextortion’
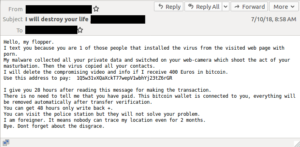
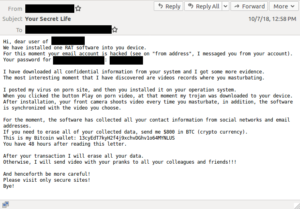
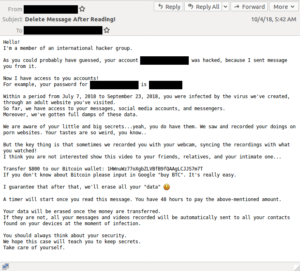
This particular kind of spam is commonly referred to as ‘sextortion’ spam. The word is a combination of sex and extortion, which is essentially what this email message is trying to do. The recurring theme we see is that the ‘hacker’ claims to have installed malware on your device, recorded you viewing porn and masturbating, and attempts to blackmail you by threatening to expose the video to your contacts unless you transfer money to a bitcoin wallet. Hence, extortion by use of sex-related material.
However, there is no evidence of these people having any such sort of video. This is more of a scare tactic used to prey on the gullible. The fact is that this scare tactic seems to be working, as evident by the transfers to the scammers’ bitcoin wallet addresses. (One would begin to wonder just what kind of people fear this blackmail spam enough to pay..)
Iterations of Sextortion Spam
The beginning iterations were basic, just as described above. However, as time went on these scammers tweaked their messages to be a little more convincing.
One tweak is claiming that they know what your password is, and may provide one in the email that truly is a password you may have used in the past.
Another tweak is providing a phone number (or last 4 digits) which may be yours, present or past.
There may be other tweaks in the future, such as knowing your name, address, etc.
How do they have my Information?
Understandably, a password or number can easily cause some stress to the recipient. Even if you don’t have a camera on your device, or if you don’t watch pornography, it is still concerning that they seem to have some of your personal information. Where did they get this?
In the information security world, unfortunately, data breaches are very frequent and sometimes in very large scale. Companies all over the world are constantly having their data exposed (both customer and employee data). These data breaches may have information such as: email address, password, phone number, address, bank card information, etc.
Past data breaches are the most likely source of data that these sextortion scammers are using to attempt to blackmail people. This is perhaps why the password or number they provide is an old one. This is so common, in fact, that we have had one of our own business email accounts compromised by a data breach in the past. This goes to show that even if you are vigilant with your security practices, a third party handling your information can still potentially leak your information (e.g. Adobe 2013, Equifax 2017).
For those curious, there is a certain website (easily found by searching “have I been pwned”) which which has the purpose of informing you whether the email address you input has been part of a data breach.
One Response to A Brief Reminder on Sextortion Spam