It is always surprising how much benefit you can get by blocking at the edge, on very simple rule sets, and how much load can be reduced. Of course it depends on your implementation, sometimes that means blocking at the router, sometimes at the operating system level, but sometimes you can have the benefit by blocking in your port handler, eg the use of “tcpwrappers” or similar software, before it gets passed off to the SMTP layer. Many forms of attack, (DDOS,Dictionary attacks via SMTP AUTH) happen that consume SMTP processes, but never actually get reported by ordinary spam protection, but it can add a lot of overhead, and consume bandwidth.
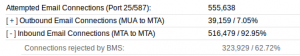
Today, we thought we would share just how much can be blocked early on. In this case, the system only uses two reputation sources, RATS-SPAM, and RATS-NOPTR. (http://spamrats.com)
RATS-SPAM is heavily laden with all the spam outbreaks happening lately from SoftLayer as well as the IP(s) detected lately in the ‘catfail’ attempts from compromised windows machines (mailcracker.exe et al), while RATS-NOPTR are from IP(s) typically from overseas, used as internet access points which have been detected as sending spam, and have no rDNS/PTR record in place, so are two of the safest lists to use at this level.
This might give you an idea what is actually consuming resources, but you never see in your regular spam protection logs. (BMS is just an efficient way to do high performance lookups, but this represents in this case, only the two reputation lists mentioned above, at an ISP with app. 10k subscribers)